
From AI to Evidence.
From Incident to Resolution
India’s Premier Digital Forensics & Incident Response Experts.
In Every Byte, the Truth Hides. We Bring It to Light. Speak to an Expert Now
From AI to Evidence.
From Incident to Resolution
India’s Premier Digital Forensics & Incident Response Experts.
In Every Byte, the Truth Hides. We Bring It to Light.
Speak to an Expert Now
Integrated Lab. Forensic Precision. Trusted Intelligence
What makes Netrika India’s leading Digital Forensics service provider?
Service Offerings
Comprehensive portfolio of DFIR services under one roof.
A Disk Image is a comprehensive duplication of a storage device, encompassing user-visible data and concealed directories, boot records, partitioned tables, deleted files, and unallocated sectors. Netrika is proficient in employing advanced tools to create precise hard disk image with proper chain-of-custody to be used in court-of-law if required.
Our Cloud-based analysis leverages advanced technology to scrutinise digital data stored in cloud environments. This efficient approach enables organisations to make informed decisions and optimise strategies based on real-time information, fostering agility and innovation in today’s dynamic business landscape.
We help uncover critical digital evidence from social media platforms using court-admissible methods. From posts and chats to deleted content and metadata, we extract and analyze data with forensic accuracy — supporting fraud investigations, civil disputes, and compliance cases with verifiable insights.
Mobile Phone Forensics encompasses a systematic digital investigative method to comprehensively scrutinise any handheld device, tablets, and satellite navigation devices, alongside their associated media like SIM cards and memory storage cards.
Network / Server forensics involves examining the network and its traffic going across a network suspected of being involved in malicious activities. With the help of network forensics, the entire data can be retrieved, including messages, file transfers, e-mails, and web browsing history, and reconstructed to expose the original transaction.
Netrika's Business Email Compromise forensic analysis uncovers the full trail of compromise—from phishing entry points to unauthorized access and data exfiltration. We analyze email headers, login patterns, and metadata to trace attackers, identify compromised accounts, and secure affected systems. Our approach ensures evidence integrity and supports legal or regulatory action.
E-mail forensics aids in scrutinising e-mail sources and content for evidentiary purposes, encompassing diverse approaches when investigating email-linked offences. Our professionals assess header data from pertinent messages, methodically decode relevant extracted details following suspect tracking, and conclude your e-mail forensic inquiry to strengthen your case.
The escalating impact of fraud and corruption and the methods employed necessitate a robust response through meticulous fact-based investigations. Acquire an in-depth, practical understanding of investigative procedures through our comprehensive program where we analyse the systems quarterly/annually. Tailored not just for internal investigators and loss prevention personnel, our pro-active approach is also beneficial for those tasked with forensic assessments within internal audit, risk, or compliance roles.
Malware forensics is essential in uncovering the origin, behavior, and impact of malicious code in compromised systems. Netrika’s expert-led service uses AI-driven analysis to trace infection paths, identify threat actors, and support effective containment. Combining automation with deep forensic insight, we deliver actionable intelligence to fortify your defenses. Designed for incident response teams, investigators, and compliance professionals facing today’s fast-evolving, AI-enabled cyber threats.
Ransomware forensics focuses on identifying attack vectors, encryption methods, and potential data recovery options. Netrika’s specialized service uses AI-powered tools to analyze system breaches, trace threat actors, and assess the full impact of ransomware incidents. Our approach helps organizations respond swiftly, recover critical data, and strengthen future defenses. Ideal for incident response, internal investigations, and compliance teams dealing with increasingly sophisticated, AI-driven ransomware threats.
Service Offerings
Core Digital Forensics
Disk Imaging & Analysis
Capturing and analyzing
storage devices
Mobile Forensics
Extracting data from
mobile devices
Cloud-based Analysis
Investigating data stored in
cloud environments
Network / Server Forensics & Analysis
Examining network and server incidents
Multimedia Forensics
Analyzing audio, video, and
image files

IoT Forensics
Analyzing data from smart devices to trace activities and breaches.
Encrypted Data Recovery & Analysis
Extracting hidden evidence from encrypted sources.

Disk Imaging & Extraction
Capturing and analyzing
storage devices
Mobile Forensics
Extracting data from
mobile devices
Cyber & Digital Forensic Lab Setup and Implementation
End-to-End Tailored configurations
to meet unique client needs
Cloud-based Analysis
Investigating data stored in
cloud environments
Network / Server Forensics & Analysis
Examining network and server incidents
Multimedia Forensics
Analyzing audio, video, and
image files

IoT Forensics
Analyzing data from smart devices to trace activities and breaches.
Encrypted Data Recovery & Analysis
Extracting hidden evidence from encrypted sources.
Incident Response & Investigations
Email Breach Investigation
Investigating unauthorized access to emails
BEC Analysis (Business Email Compromise)
Analyzing fraudulent business email attacks
Malware Forensics
Identifying and analyzing malicious software

Ransomware Forensics
Investigating and responding to ransomware incidents
Insider Threat Investigations
Uncovering threats from within organizations
Dark Web Intelligence & Monitoring
Tracking dark web activity to detect threats and data leaks.

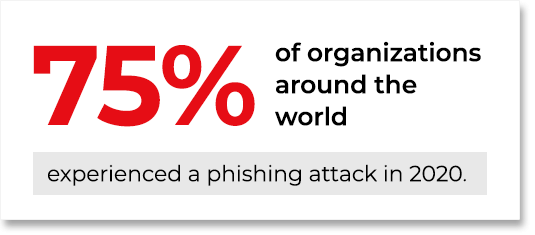
Phishing Campaign Analysis
Investigation of targeted phishing attacks, spoofed domains, and payload tracing.
BEC Analysis (Business Email Compromise)
Analyzing fraudulent business email attacks
Malware Forensics
Identifying and analyzing malicious software

Ransomware Forensics
Investigating and responding to ransomware incidents
Insider Threat Investigations
Uncovering threats from within organizations
Dark Web Intelligence & Monitoring
Tracking dark web activity to detect threats and data leaks.

Phishing Campaign Analysis
Investigation of targeted phishing attacks, spoofed domains, and payload tracing.
Log Analysis
Investigating incidents and threats through system log data.
Governance, Risk & Compliance

Forensic Readiness
Assessment
Evaluating preparedness
E-Discovery
Managing electronic data as legal evidence

Digital Forensic Trainings
Uncover evidence, trace threats, and recover encrypted data.

Forensic Readiness Assessment
Evaluating preparedness
E-Discovery
Managing electronic data as legal evidence
Data Hygiene and Sanitisation
Keeping your data clean, accurate, compliant, validated, and relevant to your operations.

Digital Forensic Trainings
Uncover evidence, trace threats, and recover encrypted data.

Chain of Custody & Documentation
Ensuring the integrity of evidence and maintaining accurate case records.
Expert Witness Testimony
Specialist insights guiding legal outcomes in compliance matters.
Core
Digital Forensics

Disk Imaging & Extraction
Capturing and analyzing
storage devices
Mobile Forensics
Extracting data from
mobile devices
Cloud-based Analysis
Investigating data stored in
cloud environments
Network / Server Forensics & Analysis
Examining network and server incidents
Multimedia Forensics
Analyzing audio, video, and
image files

IoT Forensics
Analyzing data from smart devices to trace activities and breaches.
Encrypted Data Recovery & Analysis
Extracting hidden evidence from encrypted sources.
Incident
Response & Investigations
Email Breach Investigation
Investigating unauthorized access to emails
BEC Analysis (Business Email Compromise)
Analyzing fraudulent business email attacks
Malware Forensics
Identifying and analyzing malicious software

Ransomware Forensics
Investigating and responding to ransomware incidents
Insider Threat Investigations
Uncovering threats from within organizations
Dark Web Intelligence & Monitoring
Tracking dark web activity to detect threats and data leaks.

Phishing Campaign Analysis
Investigation of targeted phishing attacks, spoofed domains, and payload tracing.
Log Analysis
Investigating incidents and threats through system log data.
Governance,
Risk & Compliance

Forensic Readiness Assessment
Evaluating preparedness
E-Discovery
Managing electronic data as legal evidence
Data Hygiene and Sanitisation
Keeping your data clean, accurate, compliant, validated, and relevant to your operations.

Digital Forensic Trainings
Uncover evidence, trace threats, and recover encrypted data.

Chain of Custody & Documentation
Ensuring the integrity of evidence and maintaining accurate case records.
Expert Witness Testimony
Specialist insights guiding legal outcomes in compliance matters.
Partner with Netrika for expert-driven
digital forensic solutions.
Not just a service provider — a reliable AI-powered forensic partner you can trust.

Trusted
by Fortune 100 companies, law enforcement agencies and financial institutions.

100+ years
investigative excellence

ISO 27001
compliant

Round The Clock
for incident response and resolution
Smart. Sharp. Secure.
Our forensic suite is where accuracy meets foresight
Digital Forensics Toolkit Overview
- Cellebrite UFED
- Cellebrite Inseyets
- Oxygen Forensic Detective
- Magnet Axiom Mobile
- AMPED Authenticate
- AMPED FIVE
- Speech Pro
- Passware Kit
- Elcomsoft Password Recovery
- Vound Intella Pro
- Relativity (Cloud-Based Review Platform)
- Paraben Email Examiner
- OpenText Disk Duplicator TD4
- Logicube Falcon Neo
- OpenText Tableau TX1
- X1 Social Discovery
- MALTEGO
(Windows, MacOS & Linux)
- OpenText EnCase Forensic
- Magnet AXIOM
- Exterro FTK (Forensic Toolkit)
- Paraben’s E3 Universal
- Magnet Axiom DVR Examiner
- GMDSoft MD Video
- Cellebrite Inseyets (Mobile-Specific)
- ManageEngine
- Crowdstrike Falcon Insight
Industries Served


Netrika in Numbers: Quantifying Trust, Expertise & Performance

Avg. Response Time:
Rapid mobilization exceeding industry benchmarks, ensuring faster containment.

Threat Containment Success:
Efficient isolation and neutralization of threats, minimizing impact.
Evidence Integrity:
No legal disputes over data handling, maintaining full chain-of-custody compliance.

Client Satisfaction:
Remarkable client satisfaction from post-engagement feedback surveys.

Repeat Engagements:
Strong client trust drives repeat business for proactive DFIR solutions.
The Digital Evidence Imperative – Backed by Data



Awards












Our Empanelments













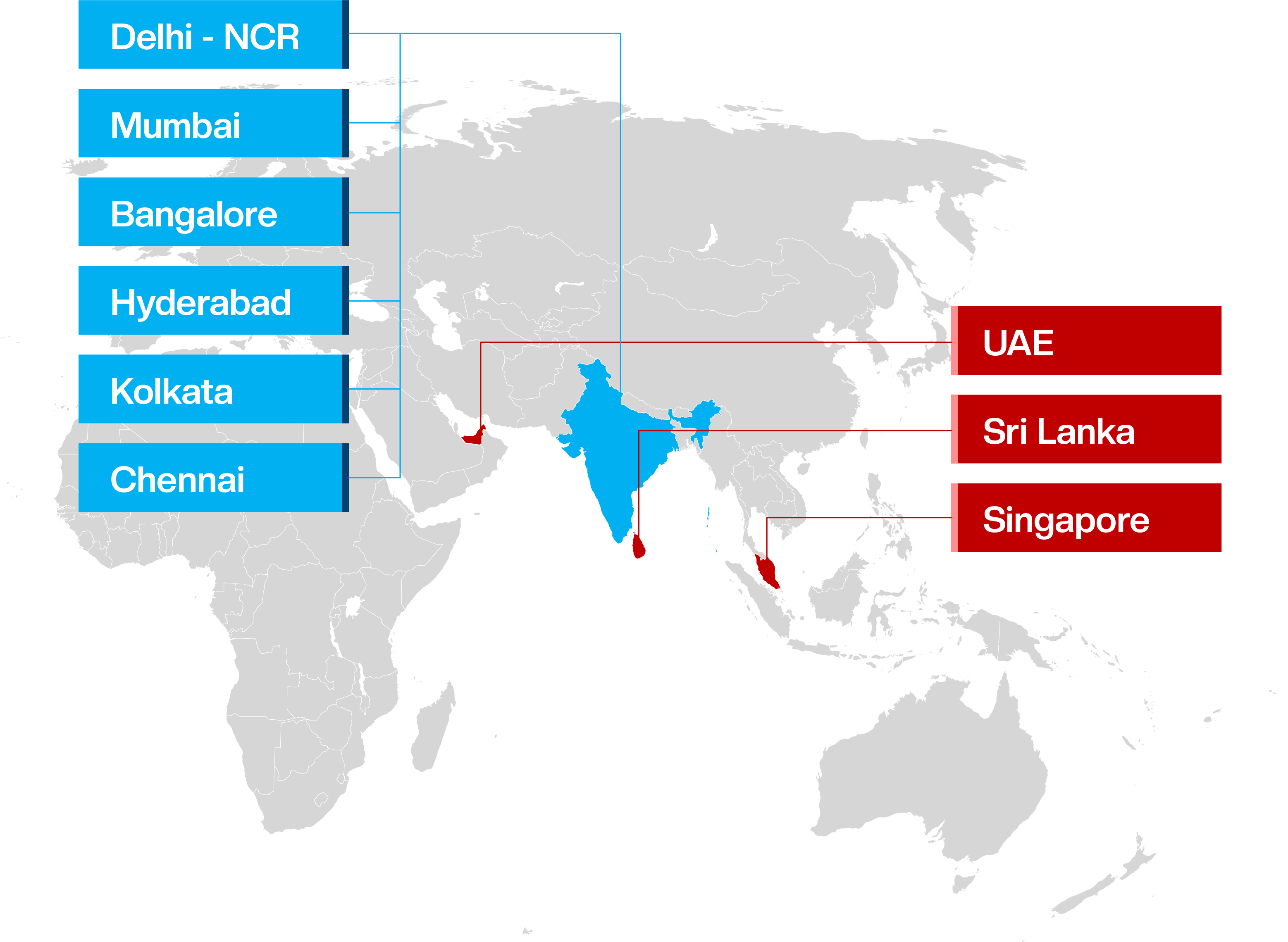
About Netrika
We are a CERT-IN empanelled and an ISO 27001:2013 certified organisation, committed to the highest standards of information security and compliance.
- Digital Forensics & Incident Response (DFIR)
- Forensic Investigations, Arbitration & Disputes
- Due Diligence
- Cyber Security
- Background Verification
- Security & Risk Consulting
- Brand Protection
- Training & Certifications
About Netrika
We are a CERT-IN empanelled and an ISO 27001:2013 certified organisation, committed to the highest standards of information security and compliance.
- Digital Forensics & Incident Response (DFIR)
- Forensic Investigations, Arbitration & Disputes
- Due Diligence
- Cyber Security
- Background Verification
- Security & Risk Consulting
- Brand Protection
- Training & Certifications
Safeguard Your Assets. Consult
with our Experts Today

1800 121 300000
info@netrika.com
Plot #2, Industrial Estate, Udyog Vihar,
Phase – IV, Gurugram 122015, Haryana, India.
Copyright © 2025 Netrika All Rights Reserved
